Table of Contents
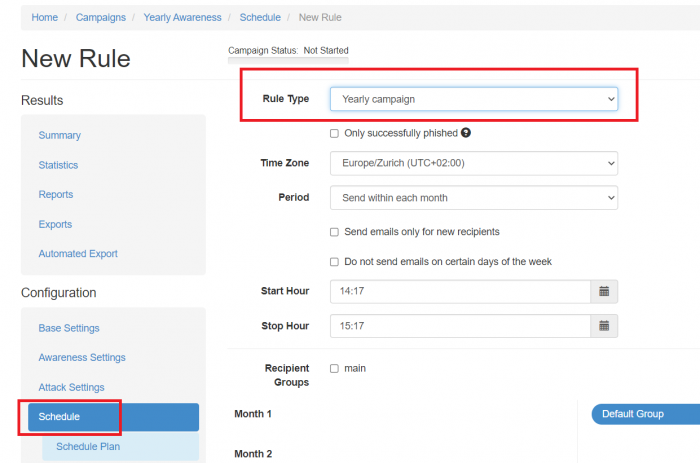
Scheduler Rule Type "Yearly Campaign"
This is a dedicated article regarding the specific Scheduler Rule Type.
More information about the Scheduler feature can be found here.
Introduction
LUCY allows you to schedule a campaign. The Yearly Campaign Rule Type mechanism provides a possibility to build an intelligent phishing campaign, testing user awareness in different scenarios over a year. The campaign can be set up once and never be stopped. The only concern would be adding the recipients to an existing group. New recipients will be automatically added to the plan starting next month. This might help to keep the security awareness of the organization at a high level and to determine the level of security knowledge among the fresh new co-workers.
The Yearly Campaign feature can be found in the section:
Campaign > Schedule > Add Rule > Rule Type > Yearly campaign
The Rule Type is available for both Phishing Scenarios with included Training and Only Awareness Campaigns.
Main Settings
- Only successfully phished: Send awareness email only to people who were successfully phished.
- Time Zone: Specify the Time Zone for the Scheduler Rule. The scheduler uses the local time & time zone. Therefore, you should make sure, that you have set the correct time & time zone before working with scheduler rules.
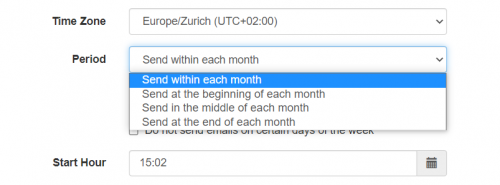
- Period: The time period of the month when the emails shall be scheduled.
Send within each month - scheduled randomly during the whole month.
Send at the beginning of each month - scheduled randomly from 1 to 9 day of the month.
Send in the middle of each month - scheduled randomly from 10 to 20 day of the month.
Send at the end of each month - scheduled randomly from 21 to end of the month.
- Send emails only for new recipients: the emails will be sent to the unprocessed recipients.
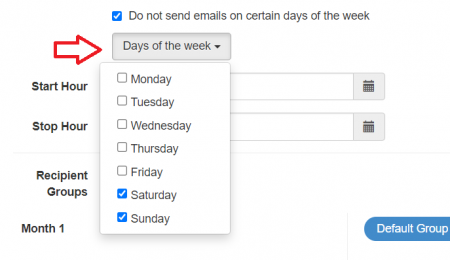
- Do not send emails on certain days of the week: determine on which days of the week the emails would not be set to the schedule. For example, select Saturday and Sunday so the recipients won't get the emails during the weekend.
- Start Hour & End Hour: define the time ranges from the beginning of email delivery until the end of email delivery. The end date will not stop the campaign. It only defines the delivery of the last message. LUCY will automatically calculate the time difference it requires to send all emails based on the number of recipients in that campaign.
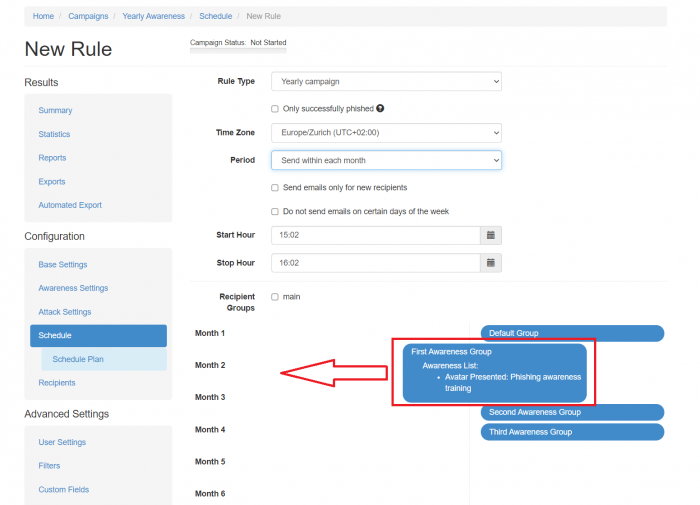
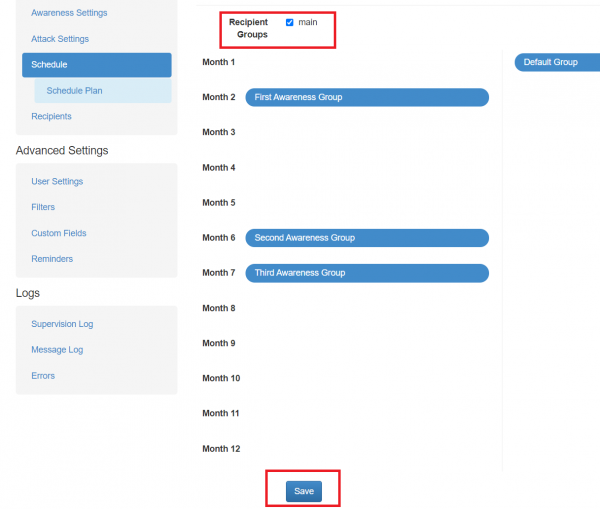
The configuration of the running scenarios per month is provided by the Drag&Drop interface after the main settings.
Drag & Drop Interface
The list of available awareness and attack scenarios in the campaign is on the right side. The list of the scenarios depends on the scenarios selected for the campaign. If the campaign type is an attack, then both kinds of scenarios are present, if the campaign is awareness only, then only awareness scenarios are being displayed.
On the left side is a list of months from 1 to 12 with an unfilled list of scenarios. The month number means the month since the new recipient has been added to the existing recipient group.
Drag a scenario from the list of scenarios (right side) to the left side and drop it over any month number. The scenario becomes visible under the corresponding month meaning that this scenario should be executed during the month according to the Scheduler Main Settings.
In case a scenario should be removed from the specific month, drag a scenario from the list of months and drop it outside this list. The scenario would disappear from the month list.
If an attack scenario is selected, there's a possibility to select an awareness scenario that should be sent in case of the recipient gets phished by the selected attack scenario.
Once the configuration is confirmed, make sure to select the recipient group and press the Save button to create the Scheduler Rule.
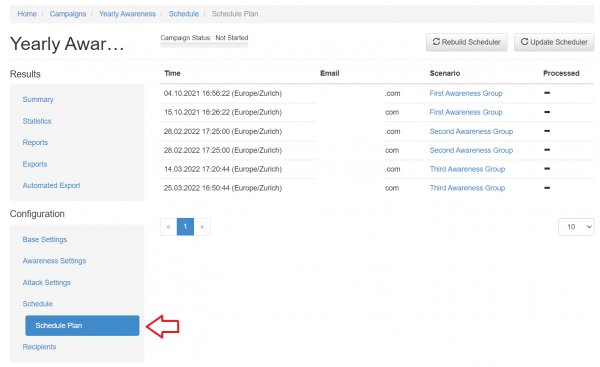
After that, the Scheduler Plan can be created and analyzed for this specific configuration.